
Modelling, Verification and Validation of the IEEE
802.15.4 for Wireless Networks
P. S. Sausen
1
, P. F. Ribeiro Neto
2
,
A. Perkusich, A. M. N. Lima, M. L. B. Perkusich
3
and F. Salvadori
1
1
Technology Department
UNIJU
´
I, Iju
´
ı - RS - Brazil
2
Informatic Department
State University of Rio Grande do Norte, Mossor
´
o - RN - Brazil
3
Electrical Engineering Department
Federal University of Campina Grande, Campina Grande - PB, Brazil
Abstract. The purpose of this paper is to present a model of an mechanism Car-
rier Sense Multiple Access - Collision Avoidance unslotted capable of accessing
the environment. This mechanism is utilized in the latest IEEE 802.15.4 stan-
dard, which defines the wireless Medium Access Control and the Physical layer-
specification for Low-Rate Wireless Personal Area Networks. For the model con-
struction, Hierarchical Coloured Petri Nets will be used. Hierarchical Coloured
Petri Nets are extensions of Coloured Petri Nets. Design/CPN tools will be used
for simulations, and the model will be verified and validated by means of occur-
rence graphs generation.
1 Introduction
The Low-Rate Wireless Personal Area Networks (LR-WPAN) is a new default in wire-
less networks developed by the Institute of Electrical and Electronic Engineers (IEEE)
and the National Institute of STandards (NIST) to transmit information to short dis-
tances at a low rate. The LR-WPAN operates within a Personal Operating Space (POS)
of 10 m or less. The LR-WPAN makes use of data rate of 20 Kb/s and an upper bound
of 250 Kb/s [1].
The LR-WPAN specified by IEEE 802.15.4 standard, is used for low cost equipment
with serious restrictions as to power consumption, the operation of which does not
require high rate transfers [2,3].
The IEEE has, recently, defined a group of established smart sensor interfaces with
the IEEE 1451.5 specifications [4]. Such specifications adopt both the ZigBee associ-
ation and the IEEE 802.15.4 technology in sensor networks applications for wireless
communication. The 802.15.4 technology defines the physical layer and the link layer,
whereas the grouping ZigBee defines the network and application layers [5].
The fast progress in the field of microprocessors, new monitoring sensors, Micro-
ElectroMechanical System and wireless communication have fostered the development
Sausen P., Neto P., Perkusich A., Lima A., Perkusich M. and Salvadori F. (2005).
Modelling, Verification and Validation of the IEEE 802.15.4 for Wireless Networks.
In Proceedings of the 3rd International Workshop on Modelling, Simulation, Verification and Validation of Enterprise Information Systems, pages 49-57
DOI: 10.5220/0002574200490057
Copyright
c
SciTePress

and application of LR-WPAN in areas related to physical, chemical and biological
processes, among others.
Due to these limitations, the search for new protocols and techniques has greatly
increased, and has become an enormous challenge in this area. Such developments,
however, require a test network that, in most cases, is not feasible from an economic
viewpoint owing to the fact that these networks are made up of hundreds, sometimes,
thousands of very expensive sensor units.
Based on what has just been said, the construction of a computational model in
order to support both the reduction in power consumption and the optimization process
has become of crucial importance in terms of costs and complexity.
It will be presented in this paper a model analysis of the IEEE 802.15.4, mainly the
link layer, by means of an access protocol to the Carrier Sense Multiple Access - Colli-
sion Avoidance (CSMA-CA) unslotted environment. Nevertheless, few are the methods
for simulating, verifying and validating such systems. Among these methods, one can
find the hierarchical coloured Petri nets. Hierarchical Coloured Petri Nets (HCPN) are
very much useful for modelling dynamic and concurrency systems, such as a wireless
sensor network.
The remaining sections of this paper have been organized as follows: Section 2 gives
full details of the mechanism CSMA-CA unslotted ; Section 3 presents a brief descrip-
tion of HCPN; Section 4 describes our Mechanism CSMA-CA unslotted HCPN model;
Section 5 presents an analysis of the model; and Section 6 exhibits the conclusions and
points towards further developments.
2 Defining the Mechanism CSMA-CA
The CSMA-CA mechanism is utilized in various network technologies, especially in
wireless technologies (e.g. in IEEE 802.ll and 802.15.4). This is a contention based-
mechanism that attempts to avoid a collision situation in the network by checking the
channel before transmission. Should the mechanism find the channel busy, a random
time, termed backoff, is then devised so as to try again until it accesses the channel;
either by reaching or even exceeding the backoff. In such cases, transmission fails, and
the frame is retransmitted [5].
The CSMA-CA algorithm cannot be used for beacon frame transmissions, acknowl-
edgement frames or data transmitted over a Contention-Free Period (CFP). The LR-
WPAN employs two different kinds of mechanism in order to access the channel: the
CSMA-CA slotted or the CSMA-CA unslotted; the CSMA-CA slotted being out of the
scope of this paper. Further information regarding this mechanism can be found in [1].
For the mechanism LR-WPAN unslotted, any devices in need of transmitting data or
Medium Access Control (MAC) commands must wait for some random time. Transmis-
sion will only be possible when the channel becomes free after the backoff; otherwise,
the device will create another backoff and attempts to access the channel once again.
Such procedure will be repeated until the channel is accessed, or until waiting upper
limits are achieved. Further details about these limits will be given later in this paper.
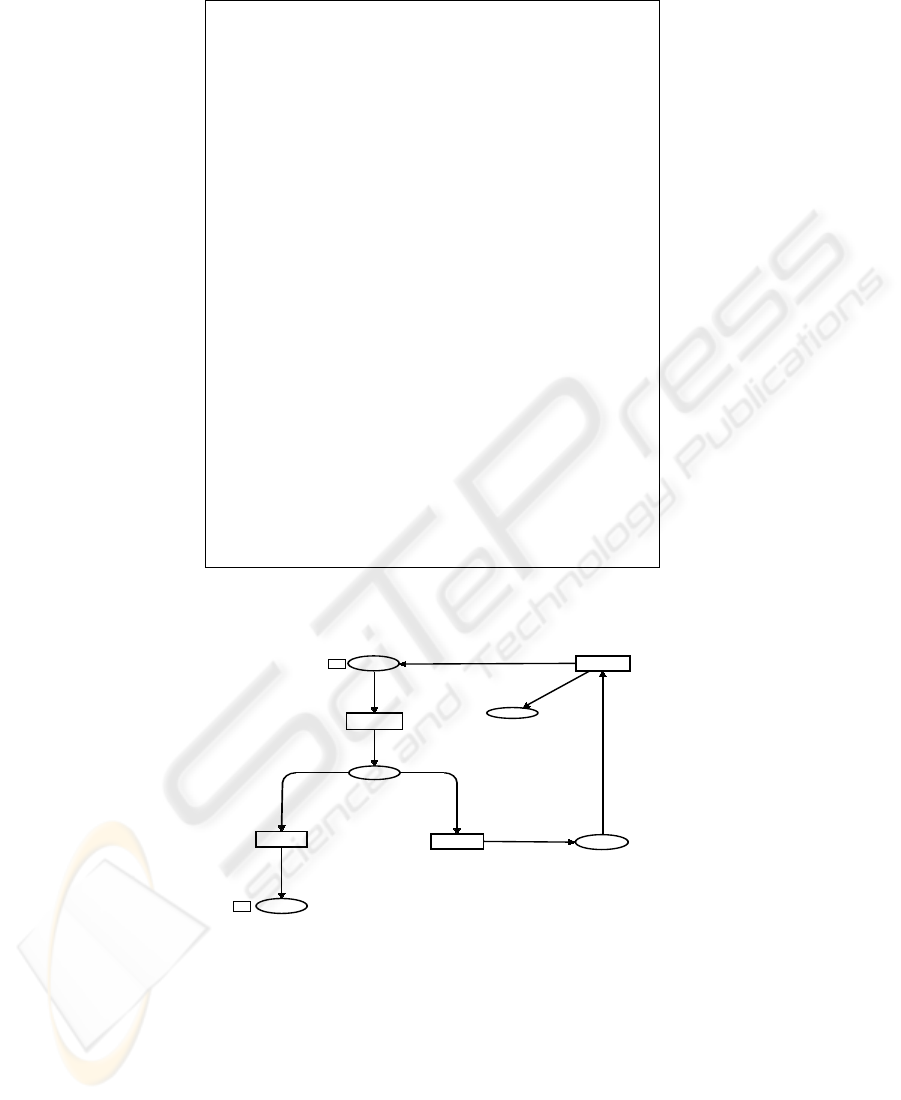
Figure 1, redrawn from [1], shows the CSMA-CA unslotted algorithm, where vari-
ables NB (Number Backoff (periods)) and BE (Backoff Exponent) are initialized in
50

CSMA-CA
unslotted
Success
Failure
Channel
Idle?
NB >
macMaxCSMA
Backoff?
NB = 0
BE = macMinBE
Delay for Random
(2
BE
- 1)
Unit Backoff Periods
Perform CCA
NB = NB +1
BE = min(BE+1, aMaxBE)
Yes
No
(1)
(2)
(3)
(4)
Yes
No
Fig.1. The CSMA-CA unslotted algorithm
step 1, with the values zero and macMinBe, respectively. The macMinBe exhibits
value 3 as default. After completion of step 2, the backoff calculation is carried out.
This can vary from zero to (2
BE
− 1) backoff units, a value that is defined by variable
aUnitBackof f period with a default value that equals 20.
Step 3 provides for the Clear Assessment (CCA). Here one verifies whether the
channel is capable of transmitting data successfully. If otherwise, step 4 will be taken,
where the NB and BE values are applied in 1. However, BE values should not be
greater than aMaxBE, whose default value is 5. Still in step 4, one verifies if the NB
value is greater or equal to the macMaxCSM ABackoff , which has the default value
for 4. If so, transmission is aborted, or returns to step 2.
CCA represents the waiting procedure defined by the backoff, which comes as a
result of the channel propagation delay, transmission delay, and other parameters, de-
pending on the physical environment. Further details can be found in [1].
3 Coloured Petri Nets Introduction
The basic foundation used for the modelling is that of the Hierarchical Coloured Petri
Nets, which is a Coloured Petri Nets extension [6]. HCPN is a suitable modelling lan-
guage used for task verification, for they can express concurrency, parallelism, non-
determinism and different levels of abstraction needed by the channel access mech-
51

anism, e.g. CSMA-CA unslotted [7]. The HCPN considers modelling at hierarchical
levels. This has been made possible by the inclusion of two mechanisms: the substitu-
tion transition, and the fusion places. A substitution transition is a transition that can be
replaced by a CPN page [6].
Modelling requires a set of computational tools for editing, simulation and analysis.
The Design/CPN [8] consists of a package of four computational tools for developing
hierarchical coloured Petri nets.
4 HCPN Model of Mechanism CSMA-CA Unslotted
The HCPN model of mechanism is described in 3 pages that models the mechanism.
There is still another page that defines the types, data structures and the functions
needed to secure its perfect functioning. The model global declarations encompass the
types and variables of the mechanisms CSMA-CA unslotted.To follow a summarized
description of these paginas will be made.
4.1 Declarations
The model global declarations encompass the types and variables of the mechanisms
CSMA-CA unslotted. Figure 2 shows all the types and variables of the model, described
as follows: BE, Backoff Exponent is the exponent used to calculate the CSMA-CA
Backoff period;VB, value Backoff is used to store the calculated value from BE and
from the random period;NB, number Backoff is used to control most backoff numbers
resulting from each transmitting cycle.
The CSMA-CA holds 4 constants that are initialized with values defined by the
IEEE 802.15.4 standard [1]. These are: macminbe which is the minimum value of BE
in the CSMA-CA algorithm; macMaxCSMABackoff which is the maximum number
of backoff; aU nitBackof fP eriod , which is the number of symbols forming the ba-
sic time period used by the CSMA-CA algorithm and amaxbe is the maximum value
attributed to the BE variable.
For the backoff calculus, a random number generator is specified by means of the
following variables: be3, be4 and be5, which are responsible for creating radom number.
4.2 Mechanism CMSA-CA Unslotted
Figure 3 shows the modelled mechanism CSMA-CA unslotted. The maximum verifica-
tion limit (macMaxCSM ABackof f) is carried out by this model by means of transi-
tions N BV alid and NBInvalid, where these have the guards [nb <> 4] and [nb = 4],
respectively. If the limit is reached, as one can see in the algorithm shown in Figure 1,
a transmission failure is then detected, in which case, the sensor is re-initiated. This is
accomplished by the arc inscription of the ReSend (1‘(sensor, 3, 0, 0))transition, after
which the verification is transmitted again; or else, the backoff calculus proceedings are
called forth by means of the CallBO place, which binds with the StartBO place, as
modelled in the BackOff Calc subpage, shown in Figure 4.
52
(* Global Declaration *)
color Sensor = with sensor1 | sensor2;
color Status = with livre | ocupado;
color Contador = int;
color BE = int;
color VB = int timed;
color NB = int;
color Tabela = product Sensor * BE * VB * NB;
color Relogio = product Status * Contador * Sensor * BE * NB timed;
var sensor:Sensor;;
var status:Status;
var cont:Contador;
var be:BE;
var vb:VB;
var nb:NB;
(* MAC SubLayer Constant *)
val macminbe = 3 : int;
val amaxbe = 5 : int;
val aunitbackoffperiod = 20 : int;
val macminbe = 3 : int;
val amaxbe = 5 : int;
val macMaxCSMABackoff = 4 : int;
(*Constant of Calculate Backoff *)
color Int_0_7 = int with 0..7;
color Int_0_15 = int with 0..15;
color Int_0_31 = int with 0..31;
var be3:Int_0_7;
var be4:Int_0_15;
var be5:Int_0_31;
( * Function for Calculate OG *)
val gettimeofday : unit -> (Int32.int * int) =
Unsafe.CInterface.c_function "SMLNJ-Time" "timeofday"
fun tod() =
let
(* max int in SML on 32 bit machines (see Int.maxInt) *);
val maxint31 = Int32.fromInt 1073741823
val (secs, _) = gettimeofday()
(* convert back into "small integers" to preserve type *)
val secs31bit = Int.fromLarge(Int32.-(secs,maxint31))
in
secs31bit
end;
Fig.2. Colors Sets and Variables
IfNB
Tabela
NBInvalid
[nb=4]
Error
Tabela
Sensors
Tabela
F
Transmit
ReSend
NBValid
[nb<>4]
CallBO
F
Tabela
TransFail
Tabela
(sensor,be,vb,nb)
(sensor,be,vb,nb)
(sensor,be,vb,nb)
(sensor,be,vb,nb)
1‘(sensor,3,0,0)
(sensor,be,vb,nb)
(sensor,be,vb,nb)
(sensor,be,vb,nb)
(sensor,be,vb,nb)
Fig.3. CPN Model for CSMA-CA.
When simulation is completed, one can see, on the final marking at T ransF ail,
the number of sensors that exceeded the backoff maximum limit, and as a result, had
to initiate a re-transmission. It is on this page that sensors are inserted into our model,
53
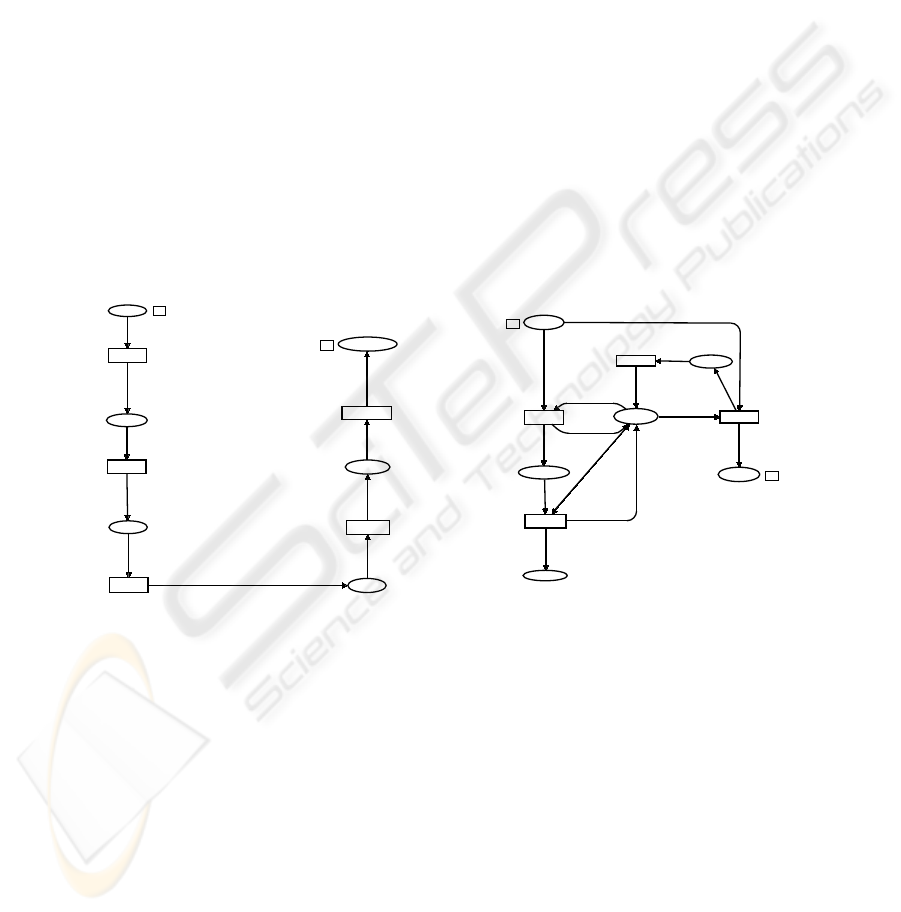
mainly, on account of the initial marking of the Sensors place. Once sensors are de-
fined, transmission is carried out with success bringing simulation to an end in a case
where no feedback was needed.
The fusion place of the CSMA−CA page was obtained through an AccessChannel
subpage whose description can be found in Section 4.4. This will supply this page with
the sensors’ traffic. The latter will find the busy channel after a backoff initial period.
4.3 BackOffCalc
The BackOf f page, shown in Figure 4, models the backoff calculus procedure. This
page is summoned by CSM A − CA page from which it obtains the sensors’ traffic,
going through steps 1, 2 and 3 of the algorithm shown in Figure 1. The CaseBE and
CompBE transitions arcs work out the BE calculus and determine the random waiting
value. Both are shown in step 2 of Figure 1. After calculating the random time period,
the model uses up its time through the expression @+vb, which is the StarT ime transi-
tion guard. The backoff calculus procedure is completed in the SendAccChann place,
which is the fusion place with the AccessChannel page. This page will be described
in Section 4.4.
DefBe
Tabela
CompBE
AddTime
Tabela
StartTime
@+vb
BOTime
Relogio
EndBackO
ff
ConvSenso
r
Tabela
EndBOSens
or
StartBO
Tabela
F
G
CaseBE
SendAccChann
el
F
G
Tabela
(sensor,be,vb,nb)
if ((be+1) >= 5)
then 1‘(sensor,5,vb*aunitbackoffperiod,nb)
else 1‘(sensor,be+1,vb*aunitbackoffperiod,nb)
(sensor,be,vb,nb)
(livre,vb,sensor,be,nb)
(status,cont,sensor,be,nb)
(sensor,be,0,nb)
(sensor,be,vb,nb)
(sensor,be,vb,nb)
case be of
3=>1‘(sensor,be,be3,nb+1)|
4=> 1‘(sensor,be,be4,nb+1)|
5=> 1‘(sensor,be,be5,nb+1)
(sensor,be,vb,nb)
Fig.4. CPN Model for BackOffCalc.
ChFree
[status=livre]
ChAcess
Tabela
AccCh
Tabela
F
ChSend
[status=ocupado]
ChBusy
[status=ocupado]
Manage-
ment
Status
1‘livre
SendOK
Tabela
ChBusyEnd
Tabela
F
ReturnBus
y
Status
StartM
(sensor,be,vb,nb)
(sensor,be,vb,nb)
status
1‘ocupado
(sensor,be,vb,nb)
(sensor,be,vb,nb)
(sensor,be,vb,nb)
status
status
status
1‘ocupado
1‘ocupado
(sensor,be,vb,nb)
1‘livre
Fig.5. CPN Model for AccessChannel.
4.4 The AccessChannel
The AccessChannel page, described in Figure 5, is executed whenever a sensor at-
tempts to access the channel after a backoff period. The AccCh place provides the
sensors’ traffic, which is the fusion place with the SendAccChannel, as illustrated in
Figure 4. Here, the model checks if the channel is available by means of a CHF ree
transition with the guard status = f ree. Once the channel’s availability is attested, the
simulation procedure starts with the free set given by the M anagement place initial
54

marking, as shown in Figure 5. With the occurrence of CHF ree transition, a token with
a status that says busy in the Management place, will be positioned. The ChBusy
transition is then enabled, owing to its guard (status = busy). The channel remains
busy until a ChSend transition fires, indicating end of transmission.
On the other hand, whenever the ChBusy transition is enabled, it means that there
exist transmitting sensor and that the channel (ChF ree) is busy. In case one gets a
ChBusy, a token is then positioned in the ChBusyEnd place. As a result, a new
backoff calculus is needed, as this is the fusion place with StartBO, as illustrated in
Figure 4.
This page models a situation that is common to occur with the mechanism CSMA-
CA unslotted, which is a sensor to transmit and detect the busy channel. The NB is
then increased to 1, being necessary to re-calculate the backoff period, as described in
step 4 in Figure 1, and to model it on the BackOff Calc page (Fig. 4).
5 Model Analysis
For the model analysis, different scenarios have been considered in order to verify the
properties and to validate them in relation to the mechanism CSMA-CA unslotted. The
scenarios are established by the quantity of sensors defined in the model. However,
for these scenarios, two, ten and twenty sensors are taken into account. The Sensors
place initial marking corresponds to the number of sensors, as shown in Figure 3. The
model gets to its final state when all sensors, specified in the initial marking, reach the
SendOk place, as shown in Figure 5. It must be noticed that different markings may be
admitted to the final state, because a token can be represented by the color, and these
may assume different values in accordance with backoff value.
Statistics
----------------------------------------------------------
Occurrence Graph
Nodes:18448 Arcs:31036 Secs:18301 Status:Full
Boundedness Properties
----------------------------------------------------------
Best Integers Bounds Upper Lower
CSMA’AccCh 1 2 0
CSMA’AddTime 1 2 0
CSMA’ChAcess 1 1 0
CSMA’DefBe 1 2 0
CSMA’Error 1 1 0
CSMA’IfNB 1 2 0
CSMA’Management 1 1 0
CSMA’ReturnBusy 1 1 0
CSMA’SendOK 1 2 0
CSMA’Sensors 1 2 0
CSMA’Time 1 2 0
Liveness Properties
----------------------------------------------------------
Dead Markings:1400 [9986,9945,..]Dead Trans.Instances:None
As one may have noticed before, by means of occurrence graphs, it is possible to
verify the properties inherent to the model. Occurrence graphs are directed graphs that
can present a node for each reachable marking and an arc for each binding element.
An arc binds the marking node, here the associated binding element comes from the
resulting marking node of occurrence.
55

The Design/CPN graph tools will permit report emission with the general properties
of the model. This report contains information on the graph and on the properties that
are useful to understand the model’s behavior in HCPN.
Considering the scenario for two sensors, the report sent with the general properties
contains the node number, arc number, and the time needed for its full generation. The
scenario for two sensors, considered in the occurrence graph, follows as a result of
this, regarding all possible sequences including the concurrency between sensors so
as to access the channel. Should one consider only one sensor, some dead transition
instances will be identified, in which case there will be no concurrency.
As for the boundedness properties, it is important to show the following places:
Sensors, SendOK and ChAccess. For the Sensors place and SendOK the upper
and lower bounds are two and zero, respectively. These places represent the number of
sensors in the scenario. The upper bound to the place ChAcess is one, since this place
illustrates the channel, and only a sensor can access the channel.
With the liveness properties, described in the report, one can verify the absence of
dead transitions instances. For such, the number of dead markings is identified as a state
explosion, due to the acceptable backoff number. This is shown in Section 4.
With the various simulations covering the scenarios two, ten and twenty sensors,
one may deduce that the model presents only correct end states and deadlock free. The
correct end states are illustrated by the SendOK place, shown in Figure 5, where all
sensors for the final simulation are to be found.
The properties considered above are significant for validating the model, for the
channel represented by the ChAccess place can only have one sensor at a time. The
SendOK shows the sensors that were successfully transmitted.
6 Conclusions
The main contribution of the present research is the setting up of a formal model def-
inition, using Coloured Petri Nets for the IEEE 802.15.4 Link Layer. By means of this
model, it will be possible to develop techniques for the reduction of power consumption
and for the optimization process.
The model we propose to represent such standard proved to be coherent. The model
was checked by means of an occurrence graph tool through which each place maximum
and minimum markings were obtained. It was also possible to investigate transmission
failure occurrences by a final marking of the T ransF ail place, i.e. when a sensor at-
tempts to access the medium four times over, only to find it busy. The model validation
is obtained by the final marking of the SendOK place. At the end of simulation, all
items specified by the initial marking must be presented this place, in spite of the fact
that some attributes may exhibit different values. By means of these values, it is possible
to verify the network loading state.
References
1. : 802.15.4-2003 IEEE Standard for Information Technology-Part 15.4: Wireless Medium Ac-
cess Control (MAC) and Physical Layer (PHY) Specifications for Low Rate Wireless Personal
Area Networks (LR-WPANs). (2003)
56

2. Howitt, I., Gutierrez, J.A.: IEEE 802.15.4 Low Rate Wireless Personal Area Network Coex-
istence Issues. WCNC 2003 - IEEE Wireless Communications and Networking Conference 4
(2003) 1481–1486
3. Zheng, J., Lee, M.J.: Will IEEE 802.15.4 Make Ubiquitous Networking a Reality: A Discus-
sion on a Potential Low Power, Low Bit Rate Standard. Communications Magazine, IEEE 42
(2004) 140–146
4. Sausen, P.S., Rocha-Neto, J.S.: The State of Art the Standard IEEE 1451(In Portuguese). I
Workshop of the Net of Instrumentation and Control (2004)
5. Callaway, E.H.: Wireless Sensor Networks: Architectures and Protocols. CRC Press LLC,
New York (2003)
6. Jensen, K.: An introduction to the practical use of coloured petri nets. In: Lectures on Petri
Nets II: Applications. Springer (1998)
7. Gordon, S.D.: Verification of the WAP Transaction Layer using Petri Nets. PhD thesis,
University of South Australia, Adelaide, South Australia (2001)
8. Jensen, K., al, e.: ”Design/CPN” 4.0. Meta Software Corporation and De-
partment of Computer Science, University of Aarhus, Denmark. (1999) On-line ver-
sion:http://www.daimi.aau.dk/designCPN/.
57
